
Kurt Pan 密码周刊 (38)
1Papers
本周ePrint上文章可谓是异彩纷呈,从这个时间点看,绝大部分上传的高质量有意思文章应该都是Asiacrypt 2021的录用文章。
Post-Quantum Signal Key Agreement with SIDH
https://eprint.iacr.org/2021/1187.pdf Interhead Hydra Two Heads are Better than One
https://eprint.iacr.org/2021/1188.pdf Simple Constructions from (Almost) Regular One-Way Functions
https://eprint.iacr.org/2021/1192.pdf Do you feel a chill? Using PIR against chilling effects for censorship-resistant publishing
https://eprint.iacr.org/2021/1195.pdf ()-indistinguishable Mixing for Cryptocurrencies
https://eprint.iacr.org/2021/1197.pdf KDM Security for the Fujisaki-Okamoto Transformations in the QROM
https://eprint.iacr.org/2021/1200.pdf The irreducible vectors of a lattice: Some theory and applications
https://eprint.iacr.org/2021/1203.pdf Attacks on Pseudo Random Number Generators Hiding a Linear Structure
https://eprint.iacr.org/2021/1204.pdf Efficient Perfectly Secure Computation with Optimal Resilience
https://eprint.iacr.org/2021/1206.pdf Non-Malleable Vector Commitments via Local Equivocability
https://eprint.iacr.org/2021/1207.pdf On Actively-Secure Elementary MPC Reductions
https://eprint.iacr.org/2021/1208.pdf Simple and Efficient Batch Verification Techniques for Verifiable Delay Functions
https://eprint.iacr.org/2021/1209.pdf DualRing: Generic Construction of Ring Signatures with Efficient Instantiations
https://eprint.iacr.org/2021/1213.pdf Black-Box Impossibilities of Obtaining 2-Round Weak ZK and Strong WI from Polynomial Hardness
https://eprint.iacr.org/2021/1214.pdf Elliptic Curve Fast Fourier Transform (ECFFT) Part I: Fast Polynomial Algorithms over all Finite Fields
https://arxiv.org/pdf/2107.08473.pdf Algebraic Adversaries in the Universal Composability Framework
https://eprint.iacr.org/2021/1218.pdf Towards Tight Adaptive Security of Non-Interactive Key Exchange
https://eprint.iacr.org/2021/1219.pdf Digital Signatures with Memory-Tight Security in the Multi-Challenge Setting
https://eprint.iacr.org/2021/1220.pdf Simple, Fast Malicious Multiparty Private Set Intersection
https://eprint.iacr.org/2021/1221.pdf Fault-enabled chosen-ciphertext attacks on Kyber
https://eprint.iacr.org/2021/1222.pdf Generalized Pseudorandom Secret Sharing and Efficient Straggler-Resilient Secure Computation
https://eprint.iacr.org/2021/1223.pdf Trojan-Resilience without Cryptography
https://eprint.iacr.org/2021/1224.pdf Succinct LWE Sampling, Random Polynomials, and Obfuscation
https://eprint.iacr.org/2021/1226.pdf Computational Robust (Fuzzy) Extractors for CRS-dependent Sources with Minimal Min-entropy
https://eprint.iacr.org/2021/1228.pdf Direct Product Hardness Amplification
https://eprint.iacr.org/2021/1229.pdf Two-Round Maliciously Secure Computation with Super-Polynomial Simulation
https://eprint.iacr.org/2021/1230.pdf Estimating (Miner) Extractable Value is Hard, Let’s Go Shopping!
https://eprint.iacr.org/2021/1231.pdf Gröbner Basis Attack on STARK-Friendly Symmetric-Key Primitives: JARVIS, MiMC and GMiMCerf
https://eprint.iacr.org/2021/1232.pdf Blockchains Enable Non-Interactive MPC
https://eprint.iacr.org/2021/1233.pdf Policy-Compliant Signatures
https://eprint.iacr.org/2021/1234.pdf Hierarchical Integrated Signature and Encryption
https://eprint.iacr.org/2021/1237.pdf Quantum Linearization Attacks
https://eprint.iacr.org/2021/1239.pdf Count Me In! Extendability for Threshold Ring Signatures
https://eprint.iacr.org/2021/1240.pdf Shuffling Public Keys (A Peer-to-peer Voting Algorithm)
https://eprint.iacr.org/2021/1241.pdf Non-Interactive Differentially Anonymous Router
https://eprint.iacr.org/2021/1242.pdf Syndrome Decoding Estimator
https://eprint.iacr.org/2021/1243.pdf Astrolabous: A Universally Composable Time-Lock Encryption Scheme
https://eprint.iacr.org/2021/1246.pdf A Geometric Approach to Linear Cryptanalysis
https://eprint.iacr.org/2021/1247.pdf Flexible Anonymous Transactions (FLAX): Towards Privacy-Preserving and Composable Decentralized Finance
https://eprint.iacr.org/2021/1249.pdf Efficient NIZKs for Algebraic Sets
https://eprint.iacr.org/2021/1251.pdf EasyPQC: Verifying Post-Quantum Cryptography
https://eprint.iacr.org/2021/1253.pdf Vector and Functional Commitments from Lattices
https://eprint.iacr.org/2021/1254.pdf How to Find Ternary LWE Keys Using Locality Sensitive Hashing
https://eprint.iacr.org/2021/1255.pdf Oblivious Messsage Retrieval
https://eprint.iacr.org/2021/1256.pdf Bit Security as Computational Cost for Winning Games with High Probability
https://eprint.iacr.org/2021/1258.pdf Parallel Repetition of -Special-Sound Multi-Round Interactive Proofs
https://eprint.iacr.org/2021/1259.pdf Identity-Based Encryption for Fair Anonymity Applications: Defining, Implementing, and Applying Rerandomizable RCCA-secure IBE
https://eprint.iacr.org/2021/1261.pdf Reverse Firewalls for Adaptively Secure MPC without Setup
https://eprint.iacr.org/2021/1262.pdf Transparency Dictionaries with Succinct Proofs of Correct Operation
https://eprint.iacr.org/2021/1263.pdf Verifiably-Extractable OWFs and Their Applications to Subversion Zero-Knowledge
https://eprint.iacr.org/2021/1264.pdf Special Soundness in the Random Oracle Model
https://eprint.iacr.org/2021/1265.pdf Tight Quantum Indifferentiability of a Rate-1/3 Compression Function
https://eprint.iacr.org/2021/1267.pdf Simulation-Based Bi-Selective Opening Security for Public Key Encryption
https://eprint.iacr.org/2021/1268.pdf Practical Continuously Non-Malleable Randomness Encoders in the Random Oracle Model
https://eprint.iacr.org/2021/1269.pdf Speak Much, Remember Little: Cryptography in the Bounded Storage Model, Revisited
https://eprint.iacr.org/2021/1270.pdf Efficient CCA Timed Commitments in Class Groups
https://eprint.iacr.org/2021/1272.pdf A note on a Claim of Eldar & Hallgren: LLL already solves it
https://github.com/lducas/BDD-note
SAC 2021
https://www.sac2021.ca/home
MAYO: Practical Post-Quantum Signatures from Oil-and-Vinegar Maps Simple and Memory-efficient Signature Generation of XMSS^MT Zaytun: Lattice based PKE and KEM with Shorter Ciphertext Size Verifiable Isogeny Walks: Towards an Isogeny-based Postquantum VDF Towards Post-Quantum Key-Updatable Public-Key Encryption via Supersingular Isogenies Secret Keys in Genus-2 SIDH Improved Quantum Algorithms for the k-XOR Problem On Evaluating Anonymity of Onion Routing The Boneh-Katz Transformation, Revisited: Pseudorandom/Obliviously-Samplable PKE from Lattices and Codes and Its Application. ZKAttest: Ring and Group Signatures for Existing ECDSA Keys MPC for Access Structures over Rings and Fields
| Posts |
|---|
| Infinity Category Theory Offers a Bird’s-Eye View of Mathematics |
| 被黑 6.1 亿美金的 Poly Network 事件分析与疑难问答 |
| 安全多方计算学习路线 |
| 西电网信院陈晓峰教授团队研究成果被亚密会ASIACRYPT 2021录用 |
| 安全多方计算开源框架梳理 |
| 安全多方计算:理论、实践与应用 |
| 上海交通大学2021教书育人奖候选人展示-龙环 |
| 初识安全多方计算 |
| What does the work "An Efficient Quantum Algorithm for Lattice Problems Achieving Subexponential Approximation Factor" mean? |
| 格理论进阶之格困难问题 |
| 深入探索比特币的安全模型(上) |
| 深入探索比特币的安全模型(下) |
| GPSW06 KP-ABE 简介 |
| Videos |
|---|
| Donald Knuth: Programming, Algorithms, Hard Problems & the Game of Life |
| Post-Quantum Designated-Verifier zkSNARKs from Lattices |
| Elliptic Curve Fast Fourier Transform (ECFFT) |
| An Efficient Quantum Algorithm for Lattice Problems Achieving Subexponential Approximation Factor |
| Panel on Lattice Algorithms and Cryptography |
https://github.com/adria0/plonk-by-fingers
https://github.com/taurusgroup/multi-party-sig
https://github.com/data61/MP-SPDZ
SAC 2021 Summer School
https://www.sac2021.ca/summer-school Machine-Checked Cryptography with EasyCrypt and Jasmin - Topic 1 Secure Messaging Protocols – Then, Now, and Next- Topic 2 September 27-28, 2021 SAC 2021
https://www.sac2021.ca/program Invited Talk #1: How private is secure messaging? Invited Talk #2: Privacy-Preserving Bluetooth Based Contact Tracing --- One Size Does Not Fit All September 29 to October 01, 2021
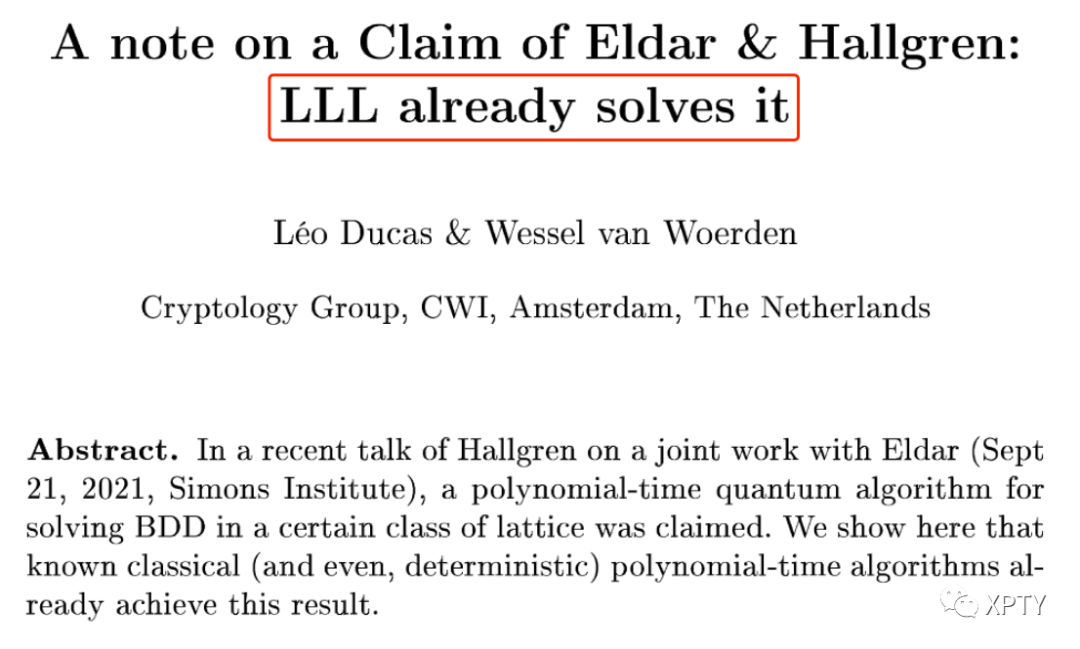
it looks like the special problem the authors address is classically easy to solve using known techniques (no quantum needed). Moreover, their core new quantum step can instead be implemented classically (and much more simply and effectively) as well. So, the work doesn’t show any quantum advantage versus what we already knew how to do classically, nor anything new about what we can do classically.
-- Chris Peikert
往期周刊回顾:
为了方便电脑用户,以及更开放的互联网访问,周刊内容会同步发布在Gitbook。
点击【阅读原文】👇可访问