
Kurt Pan 密码周刊 (21)
Part1Papers
On the Algebraic Immunity - Resiliency trade-off, implications for Goldreich's Pseudorandom Generator
https://eprint.iacr.org/2021/649.pdf Leo: A Programming Language for Formally Verified, Zero-Knowledge Applications
https://eprint.iacr.org/2021/651.pdf Smooth Zero-Knowledge Hash Functions
https://eprint.iacr.org/2021/653.pdf Non-Interactive, Secure Verifiable Aggregation for Decentralized, Privacy-Preserving Learning
https://eprint.iacr.org/2021/654.pdf Locally Reconstructable Non-malleable Secret Sharing
https://eprint.iacr.org/2021/657.pdf PipeZK: Accelerating Zero-Knowledge Proof with a Pipelined Architecture
https://www.microsoft.com/en-us/research/uploads/prod/2021/05/isca21_pizk-60a269dbb1310.pdf A Permissionless Proof-of-Stake Blockchain with Best-Possible Unpredictability
https://eprint.iacr.org/2021/660.pdf Verifying Post-Quantum Signatures in 8 kB of RAM
https://eprint.iacr.org/2021/662.pdf A Trustless GQ Multi-Signature Scheme with Identifiable Abort
https://eprint.iacr.org/2021/664.pdf AOT: Anonymization by Oblivious Transfer
https://eprint.iacr.org/2021/670.pdf zkCNN: Zero Knowledge Proofs for Convolutional Neural Network Predictions and Accuracy
https://eprint.iacr.org/2021/673.pdf Generalized Galbraith's Test: Characterization and Applications to Anonymous IBE Schemes
https://eprint.iacr.org/2021/677.pdf Efficient Attribute Based Encryption for Boolean Circuits
https://eprint.iacr.org/2021/680.pdf Batching Base Oblivious Transfers
https://eprint.iacr.org/2021/682.pdf
1CT-RSA 2021
https://sites.google.com/site/ctrsa2021/conference-program
SoK: Game-based Security Models for Group Key Exchange SoK: How (not) to Design and Implement Post-Quantum Cryptography Non-interactive half-aggregation of EdDSA and variants of Schnorr signatures Signed Diffie-Hellman Key Exchange with Tight Security Lattice-Based Proof of Shuffle and Applications to Electronic Voting More Efficient Shuffle Argument from Unique Factorization Dual lattice attacks for closest vector problems (with preprocessing) On the Hardness of Module-LWE with Binary Secret Balancing Privacy and Accountability in Blockchain Identity Management A Framework to Optimize Implementations of Matrices Oblivious TLS via Multi-Party Computation
242nd IEEE Symposium on Security and Privacy
https://www.ieee-security.org/TC/SP2021/program.html
Keep the Dirt: Tainted TreeKEM, Adaptively and Actively Secure Continuous Group Key Agreement Merkle^2: A Low-Latency Transparency Log System Post-Quantum WireGuard Red Belly: A Secure, Fair and Scalable Open Blockchain High-Frequency Trading on Decentralized On-Chain Exchanges An Interactive Prover for Protocol Verification in the Computational Model Diogenes: Lightweight Scalable RSA Modulus Generation with a Dishonest Majority Proactive Threshold Wallets with Offline Devices Compact Certificates of Collective Knowledge SoK: Computer-Aided Cryptography Lockable Signatures for Blockchains: Scriptless Scripts for all Signatures Wolverine: Fast, Scalable, and Communication-Efficient Zero-Knowledge Proofs for Boolean and Arithmetic Circuits SoK: Fully Homomorphic Encryption Compilers Pegasus: Bridging Polynomial and Non-polynomial Evaluations in Homomorphic Encryption Zero Knowledge for Everything and Everyone: Fast ZK Processor with Cached ORAM for ANSI C Programs The Provable Security of Ed25519: Theory and Practice Epochal Signatures for Deniable Group Chats BUFFing signature schemes beyond unforgeability and the case of post-quantum signatures Many-out-of-Many Proofs and Applications to Anonymous Zether
| Posts & Videos |
|---|
| 道之力:我是如何不再担心并爱上可信设置的 |
| The Limits to Blockchain Scalability |
| What everyone gets wrong about 51% attacks |
| Constant-Time Big Numbers: An Introduction |
| Mike Rosulek教授开讲不经意传输及其扩展 |
| Introducing GTC – Gitcoin’s Governance Token |
| A few lessons from the history of multiparty computation |
| Mathematicians Find Long-Sought Building Blocks for Special Polynomials |
| Blockchain voting is overrated among uninformed people but underrated among informed people |
| How Inevitable Is the Concept of Numbers? |
| Secret-shared Shuffle—秘密共享下的洗牌协议 |
| 希尔伯特计划是如何被哥德尔与图灵“打脸”的? |
| Panel:如何建设更好的 Layer2 |
| 为什么「桥」对 Layer 2 很重要? |
| 我们正从创造 NFT 转为使用 NFT,这五个领域充满机遇 |
| 随机数在区块链中的应用 |
| IEEE S&P 2021 参会小记---5月25日论文报告 |
| IEEE S&P 2021 参会小记---5月24日论文报告 |
| zkSync 1.x: Swaps, NFTs, event system, and permissionless token listing |
| Quantum computers could crack today's encrypted messages. That's a problem |
| In which I answer more quantum computing questions |
Awesome-OpenMPC: https://github.com/OpenMPC-Lab/Awesome-OpenMPC zkSummit https://www.youtube.com/playlist?list=PLj80z0cJm8QFnY6VLVa84nr-21DNvjWH7 zkSessions https://www.youtube.com/playlist?list=PLj80z0cJm8QEz6BotG4SkGSCupwkPonCZ zkStudyClub https://www.youtube.com/playlist?list=PLj80z0cJm8QHm_9BdZ1BqcGbgE-BEn-3Y Zero Knowledge Podcast https://www.youtube.com/playlist?list=PLj80z0cJm8QEUVSlofe1Zd7wyaoZrixFM The 4th ZKProof Workshop https://www.youtube.com/playlist?list=PLOEty2U8Y69Xkgt7fdNl7FtlzUcu_Ho0c
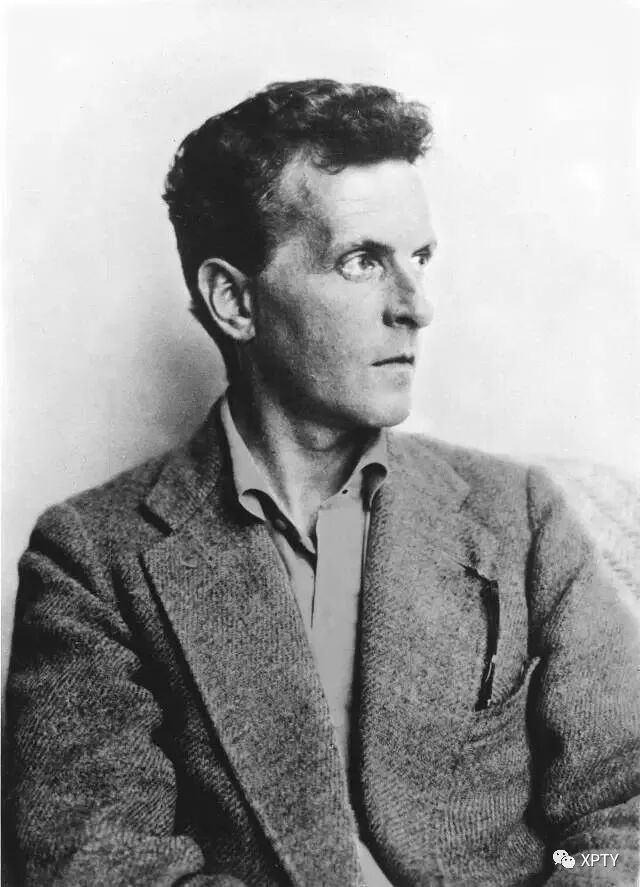
“撒谎对自己有利的时候,为什么要说实话?”
罗素转向哲学,是希望在之前只有怀疑的地方找到确定性,而维特根斯坦,则是上述那种问题激起的强制倾向把他拽进了哲学。可以说,是哲学找的他,而非他找的哲学。在他的体验里,那个问题的两难是讨厌的侵扰和费解的谜,强加于他、俘虏了他,令他不能好好过日常生活,除非哪天能用一个满意的解答将其驱除。
--《维特根斯坦传:天才之为责任》
往期周刊回顾:
为了方便电脑用户,以及更开放的互联网访问,周刊内容会同步发布在Gitbook。
点击【阅读原文】👇可访问